API Security Strategy: 8 Best Practices for Enterprise-Level Safeguarding
For large enterprises, the importance of API security cannot be overstated. Application Programming Interfaces (APIs) serve as the backbone of modern software, enabling seamless data exchange between various systems and applications. But APIs have risks, so it’s important to safeguard them from threats, unauthorized access, and data breaches. In this blog, we’ll look at 8 API security best practices proven to protect your APIs at an enterprise scale.
What is API Security?
API security means protecting APIs from unauthorized access, data breaches, and malicious activities.
At an implementation level, it involves tactics like:
- securely managing the lifecycles and versions of all API artifacts
- applying common security policies to APIs
- authentication and authorization controls
- encrypting data in transit and at rest
- setting up rate limiting to prevent abuse
- ensuring input validation to thwart common attacks
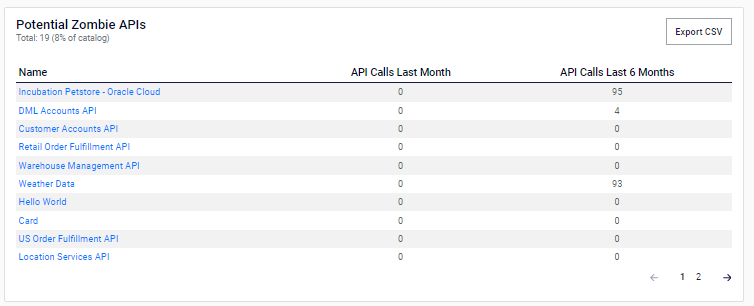
- monitoring API usage for suspicious activities as well as potential zombie APIs (those that are not being consumed and may have been forgotten about)
- regularly testing for vulnerabilities
API security is essential to safeguard sensitive data, maintain trust with users and partners, and comply with regulatory requirements in today’s interconnected digital landscape.
Here are some effective ways to include in your API security plan to safeguard your APIs on a large scale.
8 API Security Strategy Best Practices
1. Recognize the risk of APIs
It is essential to have an enterprise-wide understanding that attackers see APIs as low hanging fruit. API attacks are consistently on the rise as a result of the proliferation of APIs in recent years. 60% of companies experienced a data breach in the last two years, according to Traceable‘s 2023 API Security Report.
Increasing API sprawl within enterprises means more risk too. 100s-1000s of APIs across distributed runtimes means more shadow and zombie APIs are likely lurking in your IT infrastructure.
When implementing an API program, especially at scale, it’s important to consider API security from the outset.
2. Keep track and adapt to emerging threats
API threats are consistently evolving. Therefore, it’s important for your security stakeholders to stay up to date and adapt to the latest risks.
There are excellent online resources available to keep your teams updated. These resources include the OWASP API security top 10 vulnerabilities list and Security Boulevard’s newsletter.
In response, it’s best practice to continually update your internal security standards to stay ahead of the curve. Especially in highly regulated industries such as banking and insurance.
Fostering a collaborative approach is key too. Leverage cross-functional expertise to ensure you’re addressing security issues effectively.
3. Master API security basics
For large enterprises, it’s important to continuously enhance and update API security fundamentals. These include:
- Authentication and authorization: strict authorization practices for internal & external access to systems, data, and services.
- Validation: Monitoring Infrastructure & Ecosystems to ensure all points of access are vetted and compliant.
- Resource or rate limiting to prevent abuse: Proactively preventing improper or malicious use of Services and Applications.
- Monitoring: audit, logging, etc.: Capturing the actions and events within an Ecosystem to gain insights regarding usage & users, replicate errors, and leverage the data to make better decision going forward.
- API gateway(s): The brokers between backend services and systems to clients and applications, allowing data to be aggregated and passed quickly and securely between Channels, Enterprises, Customers, and Devices.
4. Holistic API security across the lifecycle
Your API security strategy should focus on securing APIs throughout the entire development process, in addition to the basics.
Many enterprise focus on production-only and testing security controls. Using a holistic approach throughout the API’s lifespan helps find vulnerabilities early in development, before they become a problem. This includes embedding security controls at all stages of the API lifecycle, rather than viewing them as isolated practices.
5. Automate API governance and policy enforcement
Good API security boils down to good API governance, a term often associated with slow, manual, and error-prone processes.
Automating and democratizing your API governance and policy enforcement helps with that holistic security approach we’ve just discussed.
Strong rules and guidelines can be set in the beginning and used throughout the process of creating and managing APIs. You can follow these rules and guidelines throughout the process. They are beneficial in identifying and resolving security issues. This is particularly important for developers who may not give high priority to security.
Automation ensures that APIs are well-governed and secure by default, without increased overhead. It allows each API to comply with the appropriate governance level. This ensures that APIs meet the required standards for their specific use case.
6. Improve API discovery, observability, and reporting
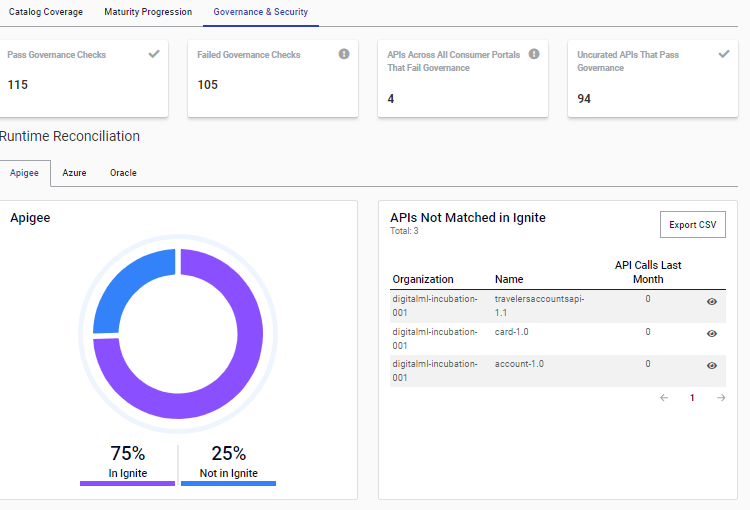
To effectively identify issues, you need to be able to keep track of all your APIs, where they’re running, and how they’re being consumed. Creating a unified view (like ignite’s Holistic Catalog provides) across multiple repos, pipelines, and runtimes is key.
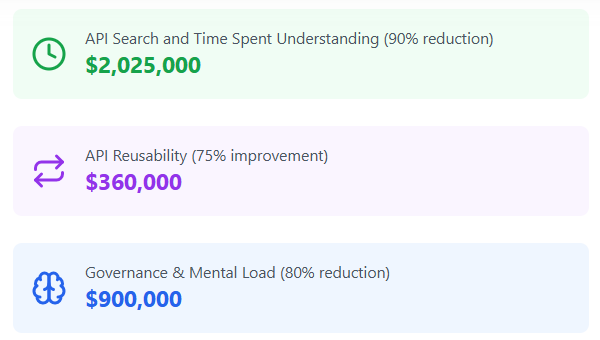
It is important to have strong reporting and metrics. This allows for easy identification of potential zombie and shadow APIs, along with other weaknesses. You can determine these weaknesses based on governance status, usage, and runtime metrics. All of this information can be found in one centralized location and acted on quickly.
Here’s an example of our ignite Platform’s governance and security reporting:
There’s another added benefit of this best practice too. From this holistic view you can identify and secure APIs passing PII (personal identifiable information) and other sensitive data; helping you improve data privacy and ultimately customer trust.
6. Consider your API architecture and tooling
To create a unified view of your API landscape for a strong API security strategy, avoid siloes caused by disconnected tools. Instead, look for providers that can seamlessly integrate with your architecture and other tooling components. For example, connecting your API catalog to lifecycle management, repos, pipelines, runtime platforms, developer portals, and other ecosystem applications e.g. ticketing and workflow platforms.
If considering an open source plugin model, there are additional factors to include in your security strategy too. Many enterprises find they need custom extensions to plugins to fit their complex use cases. Running your IP (intellectual property) through these code extensions means added risk. So does the required manual update cycles and maintenance.
7. Treat all APIs as products
APIs-as-products is a popular trend for public and monetized APIs. Applying common principles from this approach to the entire portfolio can enhance security. This change in perspective ensures that we create APIs with functionality, security, and user experience in mind. You can leverage the product mindset for enterprise security by:
- Prioritizing Security in API Design. Viewing APIs as products leads to a security-first approach in design and development. This proactive stance helps in identifying and mitigating potential security risks early in the lifecycle.
- Encouraging Continuous Improvement. Evolving APIs in terms of security features and protocols in addition to consumer feedback.
- Fostering Cross-Department Collaboration. When APIs are seen as products, it encourages collaboration between developers, security teams, and product managers. This integrated approach ensures a comprehensive security strategy encompassing all aspects of the API.
- Enhance User Experience and Trust. Prioritizing API security enhances the overall user experience, fostering trust among internal users as well as partner and external consumers. This helps you maintain a robust security posture.
In conclusion, API security is paramount in today’s digital landscape. By recognizing the risks, staying informed about emerging threats, mastering basic security measures, and adopting a holistic approach to security, you can protect your APIs and ensure the integrity of your data and systems.
Automating governance, improving API discovery, and treating APIs as products can boost API security at an enterprise level.
Book a demo with our API experts to see how the ignite Platform can help mature your API security strategy.
Differentiate Your Digital Enterprise Now
Learn how it can help your enterprise accelerate digital transformation